From time to time we need to check that VMware Distributed Port Groups are following our standard configuration. If there is only a few port group this can be done manually but in my case I need to check a few hundred.
Since there are so many I wanted to make a script that will export the configuration of each port group and out put to a CSV.
In this post we will be going through using PowerCLI to report on the configuration setting for all distributed virtual switch port groups.
I used the PowerCLI developer doc to find the required commands to check each port group configuration settings and policies.
https://developer.vmware.com/docs/powercli/latest/products/vmwarevsphereandvsan/categories/vdport/
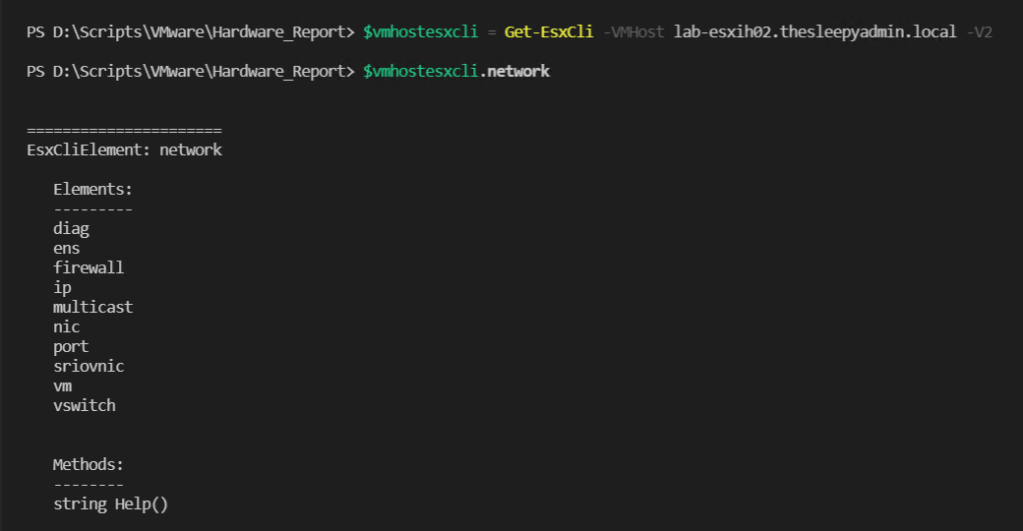
First we need to get the list of Distributed Virtual Switches (VDS)

Once we have the list of switches we can use the below command to return all port groups.
Get-VDPortgroup -VDSwitch switchname
Next we can take one port group and start to view the properties to get the required info.
The below will view the general port group settings like VLAN, port bindings and Numbers or ports.
Get-VDPortgroup -Name portgroupname |fl
To view the override policy use the below command.
Get-VDPortgroup -Name portgroupname | Get-VDPortgroupOverridePolicy
To view the teaming policy use the below.
Get-VDPortgroup -Name portgroupname | Get-VDUplinkTeamingPolicy
For team policies the name in PowerCLI is different than in the web UI, the below table will match up the names
| LoadBalancingPolicy | Load balancing |
| LoadBalanceLoadBased | Route Based on Physical NIC Load |
| LoadBalanceSrcMac | Route Based On Source MAC Hash |
| LoadBalanceSrcId | Route Based On Originating Virtual Port |
| ExplicitFailover | Use Explcit Failover Order |
| LoadBalanceIP | Route Based on IP Hash |
To view the security policy use the below.
Get-VDPortgroup -Name portgroupname | Get-VDSecurityPolicy
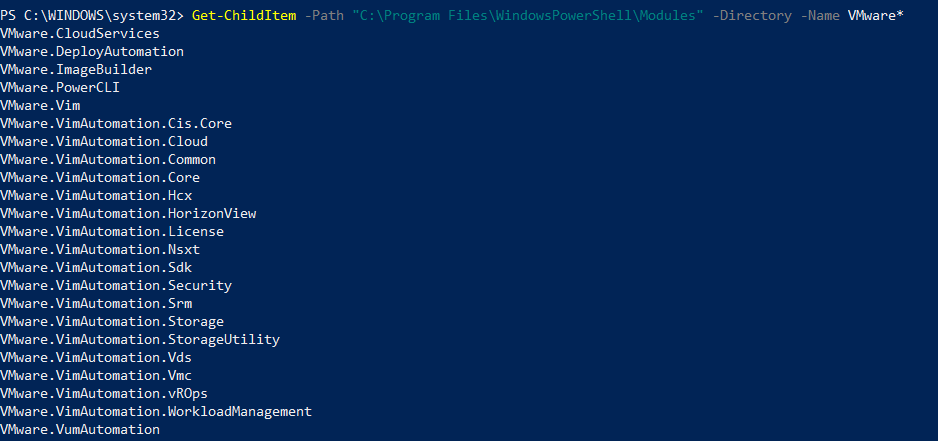
Now that I have all the different policy and configuration settings I can create the script.
I will be using a hash table for all export the configuration and policy settings.

The full script can be download from my GitHub repository link below.
https://github.com/TheSleepyAdmin/Scripts/blob/master/VMware/Network/VMwarePortGroupConfig.ps1
The script can be run to either output the configuration details to the PowerShell console using the below command.
.\VMwarePortGroupConfig.ps1 -VCServer vCenter
The second option is to export to CSV file by using the -ReportExport parameter.
.\VMwarePortGroupConfig.ps1 -VCServer vCenter -ReportExport .\
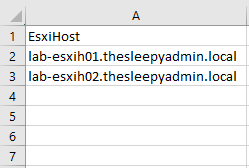
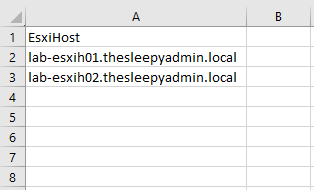
The below is what the CSV output should look like.