I setup a Windows 2019 Core server and wanted to see how well the new Windows Admin Center works. This can be installed on server core itself as it is all Web-based so I used the core server to host the WAC.
I downloaded the WAC and server Core from
https://www.microsoft.com/en-us/software-download/windowsinsiderpreviewserver
This needs an account that has signed up to windows insider program.
Once the install file is downloaded, log on to the server core console and run powershell.exe.
To copy the install to the local OS I ran
Copy-Item -Path \\serverShare\WindowsAdminCenterPreview1808.msi -Destination C:\Users\Administrator\desktop\
To install run: msiexec /i WindowsAdminCenterPreview1808.msi /qn /L*v log.txt SME_PORT=6516 SSL_CERTIFICATE_OPTION=generate or msiexec /i WindowsAdminCenterPreview1808.msi to do an interactive install. 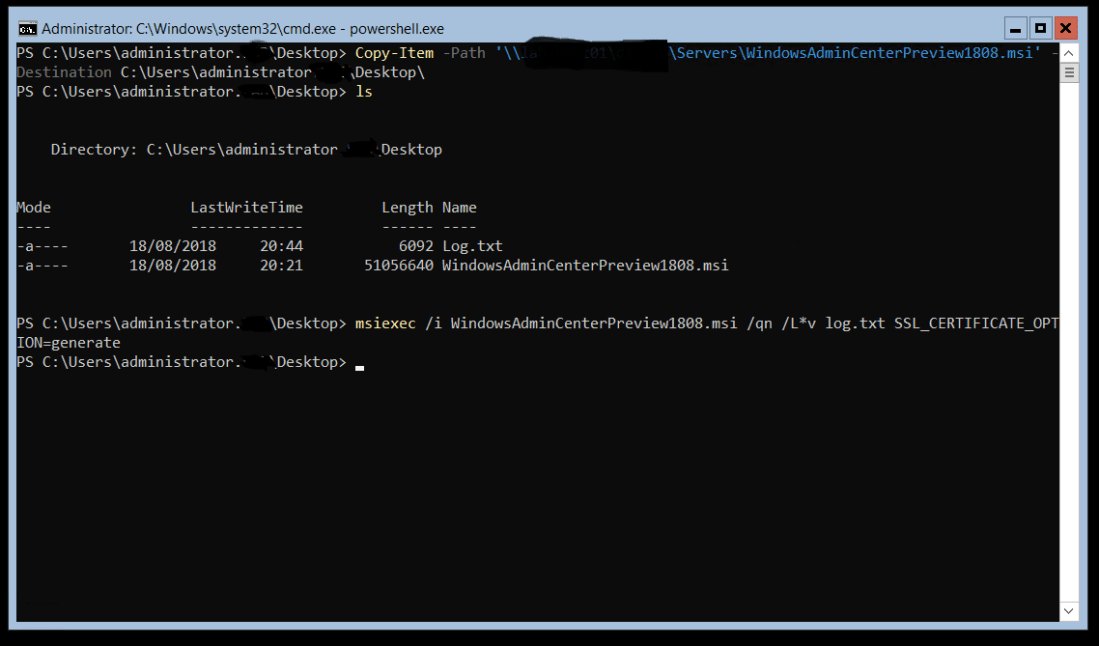 Once the install has completed you can browse to either the IP or host name of the server.
Once the install has completed you can browse to either the IP or host name of the server.
Select the server you want to manage this will then bring up all the management tools and features for that server. 











