I was upgrading our VMware SRM appliance from version 8.2 to 8.4 recently. The upgrade completed successfully but when logged on to the SRM management console and I tried to reconfigure the appliance to connect back to vCenter I started to get a error.
To get the fixes for some of the errors I had to log a case with VMware support who where very helpfully in getting the issue resolved. So decided to do a post on this in case anyone else runs in to the same issue.
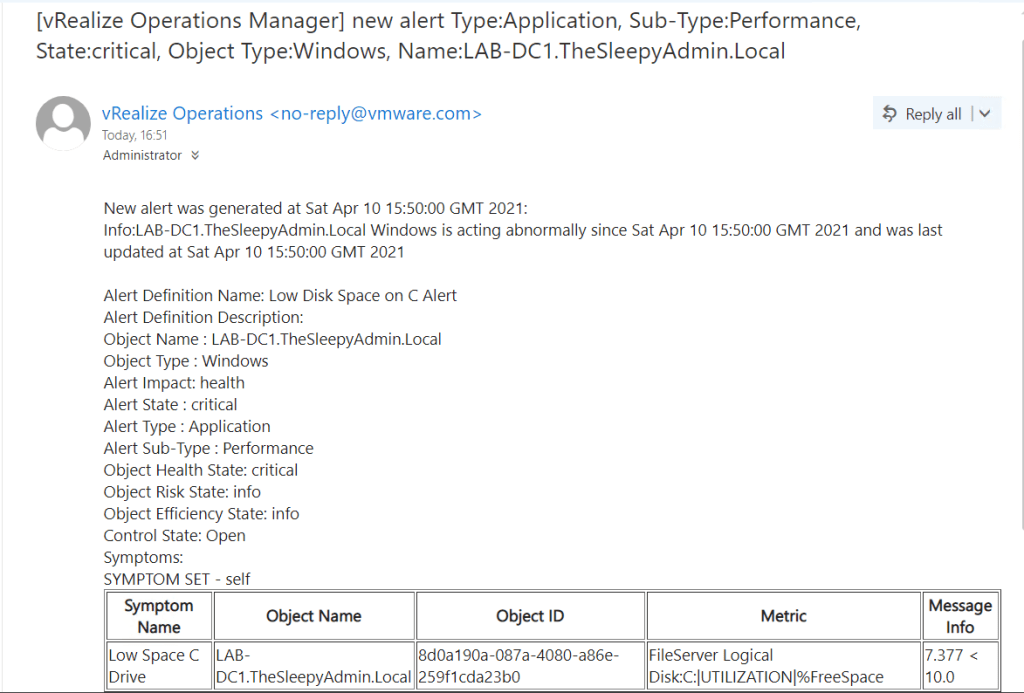
Below is the initial error I got when trying to reconnect to vCenter.

The error was about an invalid cert and failed soap response to vCenter
Exit code: 61
[backtrace begin] product: VMware vCenter Site Recovery Manager, version: 8.4.0, build: build-18048862, tag: drconfig, cpu: x86_64, os: linux, buildType: release
backtrace[03] libvmacore.so[0x001BC4BD]
backtrace[04] dr-configurator[0x00151AB4]
backtrace[05] dr-configurator[0x000663BA]
backtrace[06] dr-configurator[0x000EDCB4]
backtrace[07] dr-configurator[0x000F66FC]
backtrace[08] dr-configurator[0x000F79AF]
backtrace[09] dr-configurator[0x000F1788]
backtrace[10] dr-configurator[0x000BB3DD]
backtrace[11] libvmacore.so[0x002EFFED]
backtrace[12] libvmacore.so[0x002F1C32]
backtrace[13] libvmacore.so[0x0040327E]
backtrace[14] libpthread.so.0[0x00007F87]
backtrace[15] libc.so.6[0x000F35BF]
[backtrace end]
Caused by:
(vmodl.fault.InvalidArgument) {
faultCause = (vmodl.MethodFault) null,
faultMessage = ,
invalidProperty = “Invalid certificate”
msg = “Received SOAP response fault from []: create
“
}
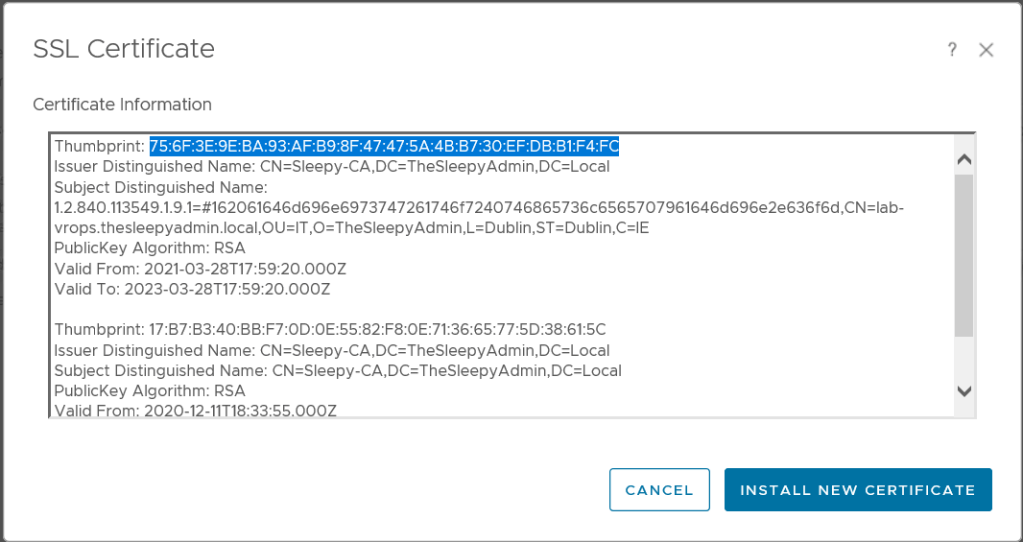
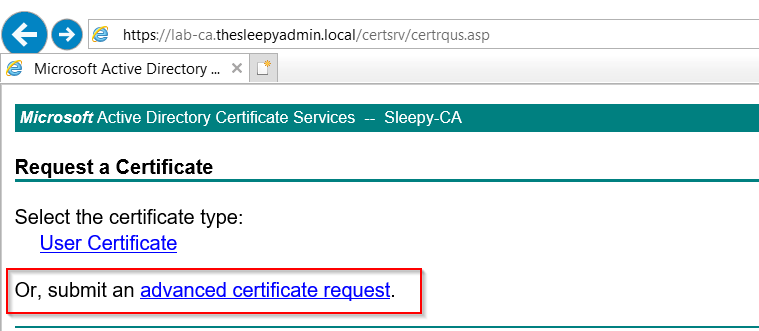
I checked the existing PSC cert in the summary page of the SRM management web client but this was fine and showing as valid, I checked the vCenter cert that was also valid so I was a bit confused as to what cert the error was actually referring to as it just said invalid certificate which isn’t all that helpful.
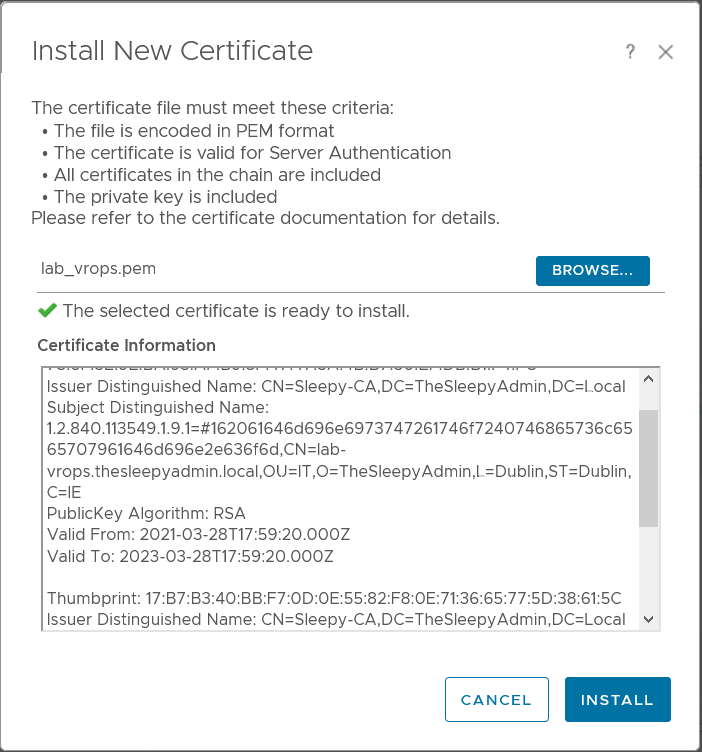
I decided to to check the appliance certificate and that had expired about 4 months ago.

To re-issue the cert we should just need to go to change and select change to reissue the cert, but my issue was that the appliance had previously been set with just a host name and not FQDN so when I tried to generate the cert I got an error for no FQDN.
It looks like the older version of SRM allows cert to be generated without FQDN’s but not version 8.4.

This was going to cause an issue with the site paring as the names had already been configure so most likely once the new cert was generated with the FQDN and connected to vCenter I would probable need to reconfigure the site paring.
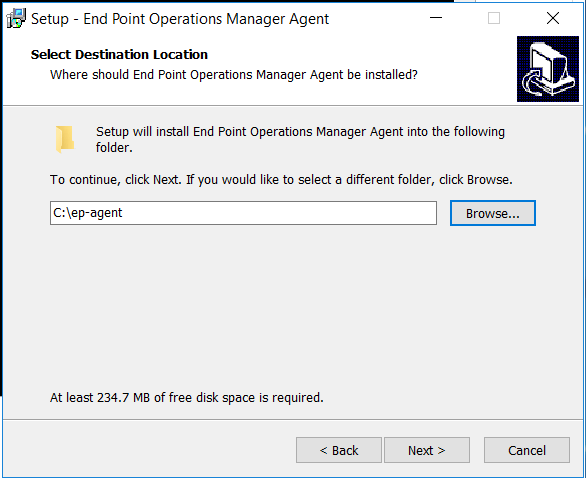
First I had to change the host name under networking to use a FQDN.

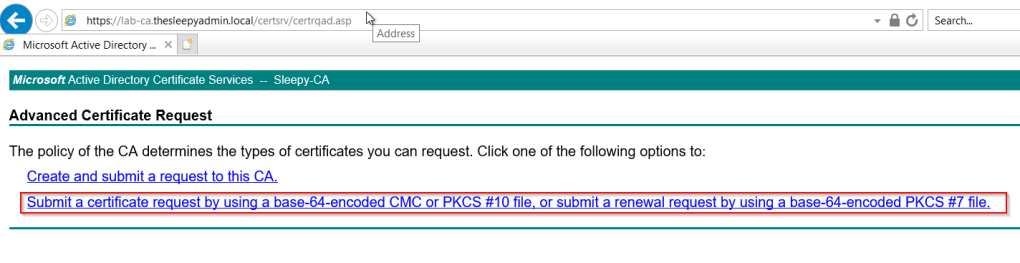
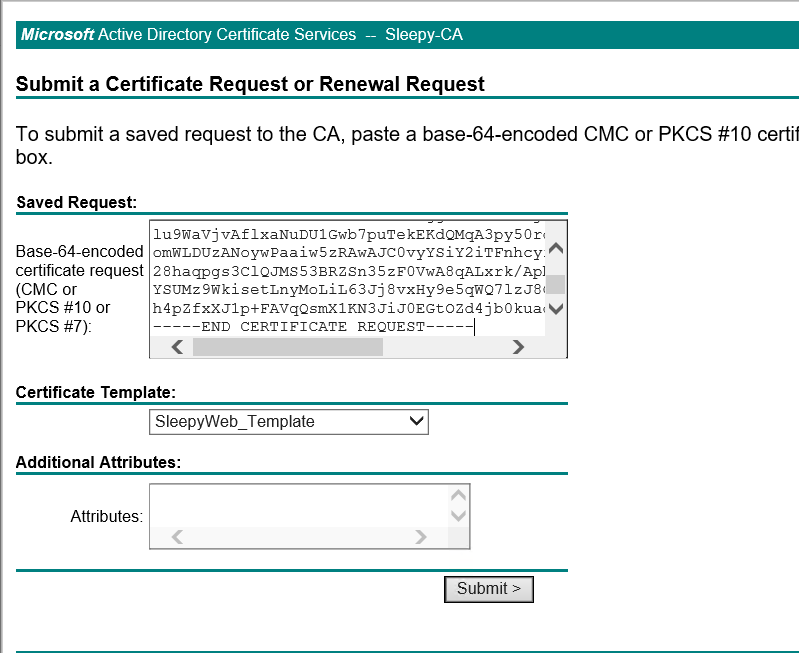
Once that was changed I tried to re-issued the self singed cert using the new FQDN name but this failed with the below error. (This is where I got stuck and had to open a service request 🙂 )
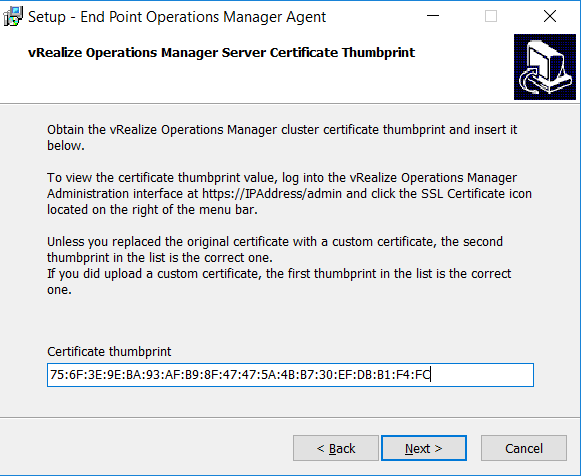
The certificate’s Subject Alternative Name does not contain one of the folowing: – an IP address that matches the SRM host IP – a DNS name that matches the SRM host name – a common Name field that matches the SRM host name.

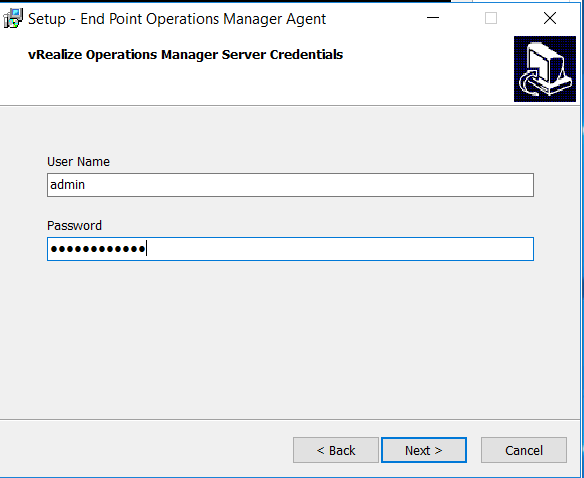
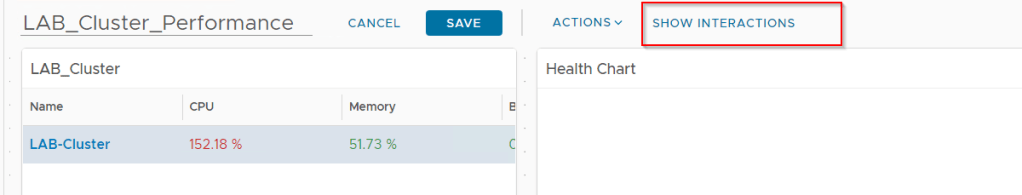
VMware support thought the issue was due to the plugin caching the old host name, so I had to then go to reconfigure on the summary page and on name and extension had to change the local host to use the new FQDN to update the plugin settings as it was set to custom and using the old host name.
The reconfigure will most likely fail due to the cert but it will update the plugin hostname which then allow the cert to be generated.

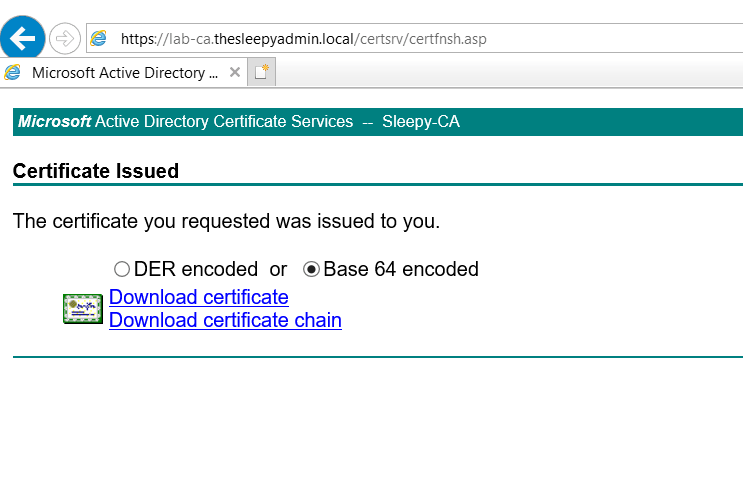
After this I was able to generate the new cert, the web console took a few minutes to come back while the cert was updated.

Once both of the above where completed SRM successfully connect back to vCenter.
After the connection was made to vCenter I had to reconnect in the SRM site pairing to update the SRM URL and certificate from the SRM UI console.

I had to complete the exact same steps on the second appliance.
This was a bit of annoying issue to get around as the errors where pretty vague and the logs didn’t really give much information.
Hopefully the rest of my upgrade goes a bit smother than the SRM upgrade.