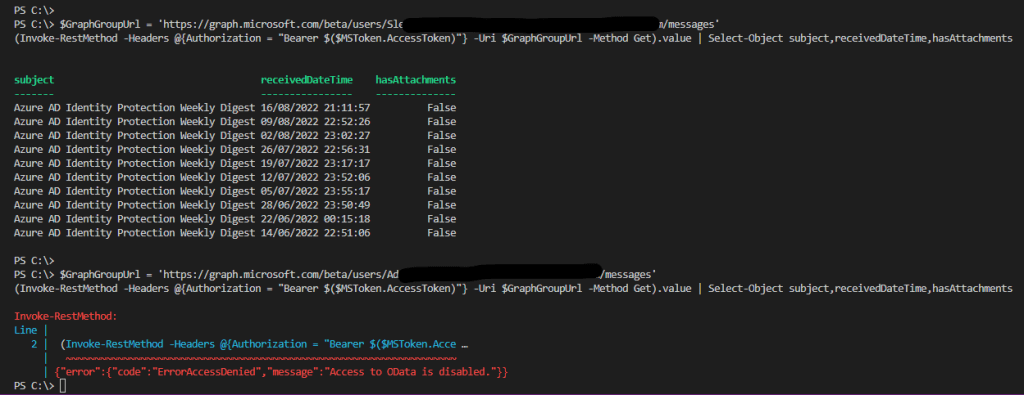
Recently we have been reviewing some of our old Exchange Web Service mailbox connections and updating these to use Microsoft Graph. We wanted to restrict what mailbox’s the Azure App registration used for Microsoft Graph could connect to.
To set this up in Exchange Online we can use an Application Access Policy. In this post we will be going through setting up and confirming the mailbox’s access.
I have gone through setting up Azure App registration for Microsoft Graph before so we wont be going through that in this post.
I will also be using certificate and Microsoft MSAL PowerShell Module to get the Graph access token.
See post below if you need to know how to connect using MSAL with certificate base authentication.
Once we have the app registration setup and certificate issued and uploaded to the app registration, we can then assign the GaphApi permission to access mailboxes.
If we don’t apply the permission we will get access denied.

I will be giving Mail.Read API permission, this will give access to view all mailboxes.

Grant admin consent for the API permission.
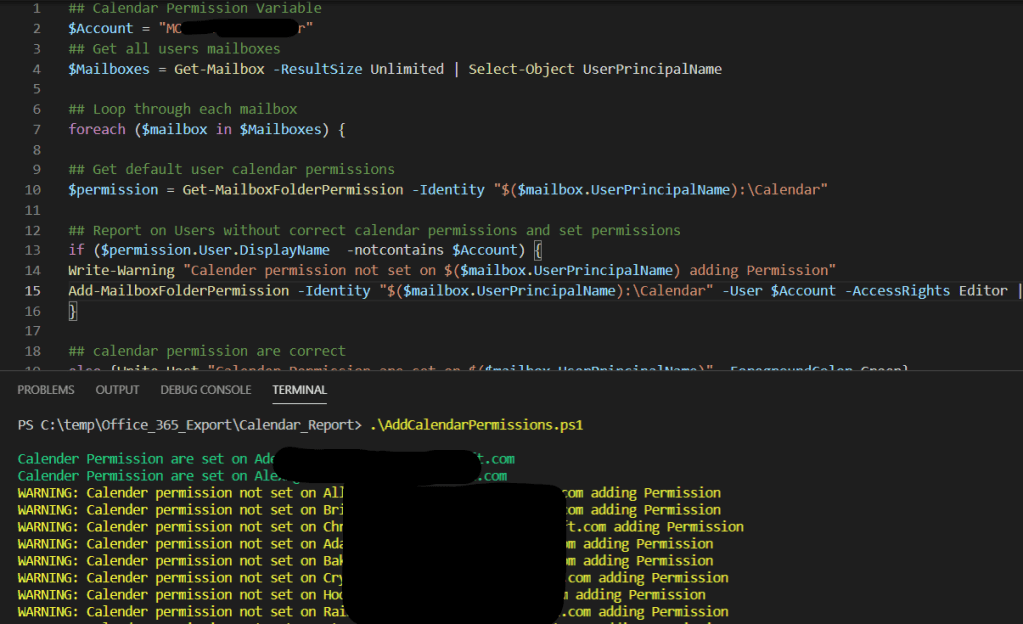
Now if we try to query the mailbox we should now be able to see the messages.
At this stage we can use the App registration to read messages from any mailboxes.
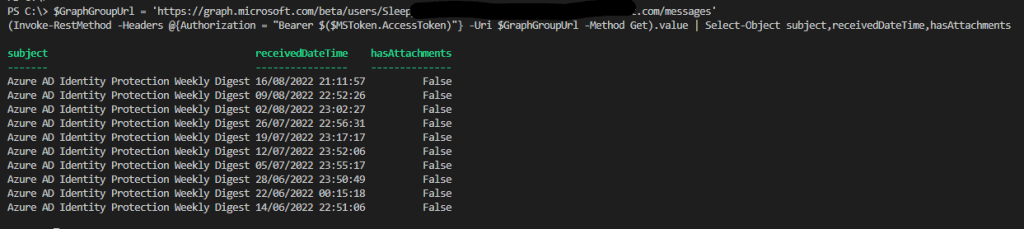
To lock this down so that the Graph query is only able to view certain mailboxes we can use
New-ApplicationAccessPolicyto create an application access policy. The policy can be applied to a group or a single users.
To run the command, we will need Application ID of the app registration, mailbox or mail enabled security group and description. Using a group is useful if there are multiple mailboxes that they will need to allow access.
New-ApplicationAccessPolicy -AppId ApplicationID -PolicyScopeGroupId "user_group@domain.com" -AccessRight RestrictAccess -Description "Restrict this app to view mailbox or security group."To run the command we need to connect to Exchange Online
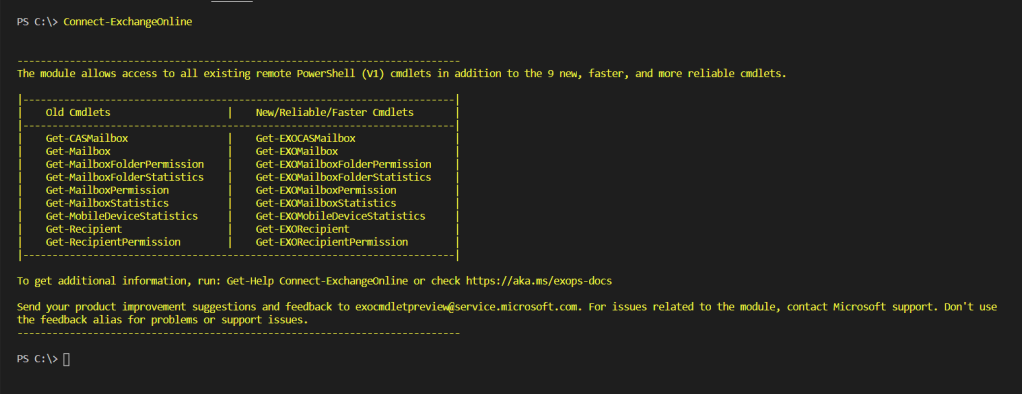
Connect-ExchangeOnlineThen run the command to create the application access policy.
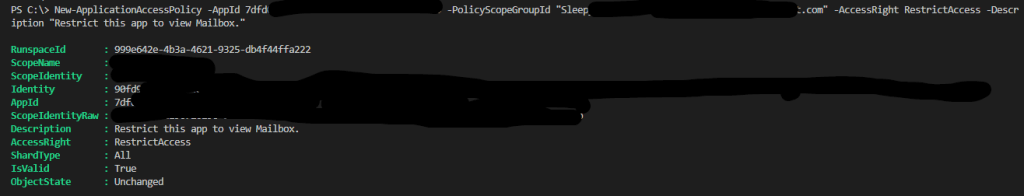
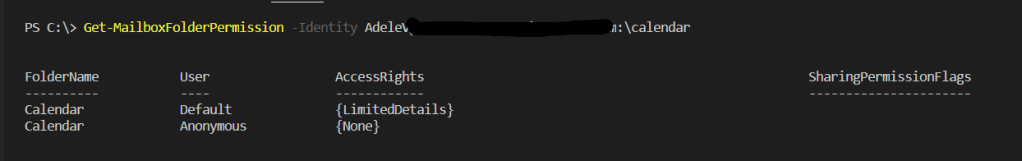
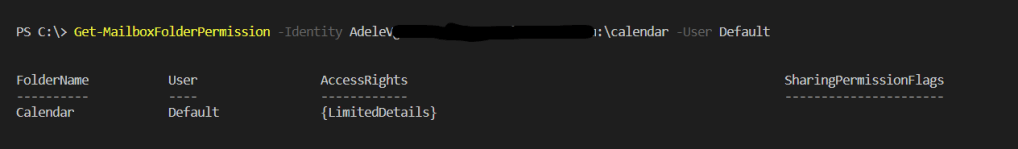
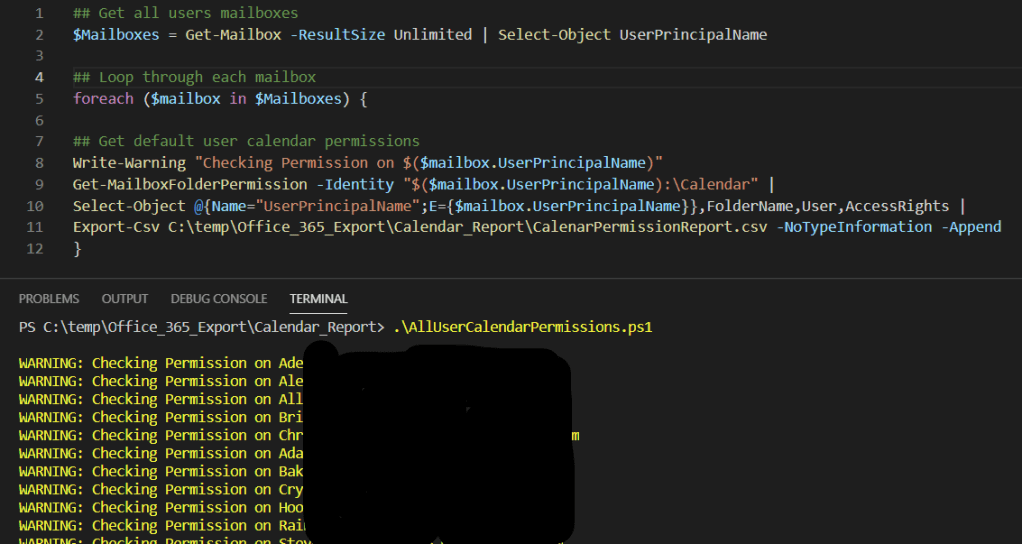
We can test what mailboxes the app registration can access using.
Test-ApplicationAccessPolicy -AppId ApplicationID -Identity user_group@domain.local
Now once we try to query the mailbox we have give access to we will see the message returned, if we try query any other mailbox we will an error message.
Applying the application access policy is a good idea for security as allowing an application to read mailboxes that it doesn’t need access to can be a risk if the app was ever compromised or there is sensitive data in mailboxes that no other users or application should have access to.