Today I was setting up Integrated Windows Authentication single sign on for an Azure Application proxy that connects to an internal Apache web application.
We had already configured the application for SSO internally.
Below is the link to the Kerberos SSO for Azure App Proxy
Prerequisites
Before you get started with single sign-on for IWA applications, make sure your environment is ready with the following settings and configurations:
- Your apps, like SharePoint Web apps, are set to use Integrated Windows Authentication. For more information, see Enable Support for Kerberos Authentication.
- All your apps have Service Principal Names.
- The server running the Connector and the server running the app are domain joined and part of the same domain or trusting domains.
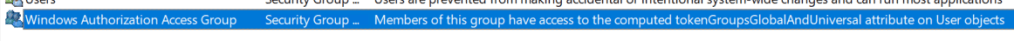
- The server running the Connector has access to read the TokenGroupsGlobalAndUniversal attribute for users.
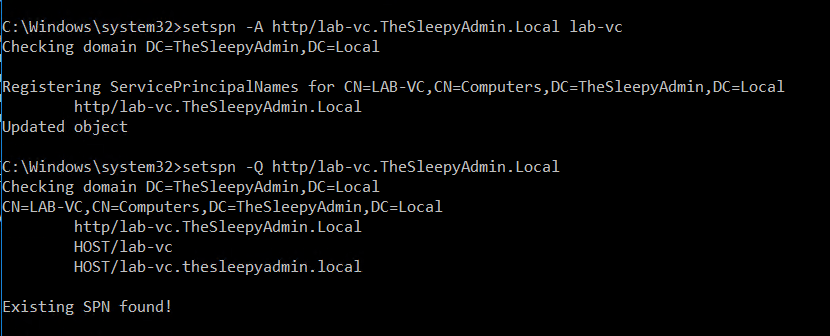
First step was to confirm that there was an SPN configured for the Application. Since this is a web application we will use http for the serviceclass.
setspn -Q http/webapp.domain.local
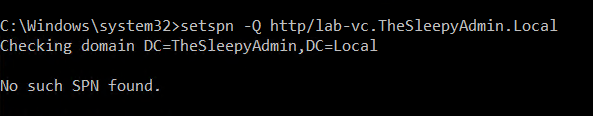
If the SPN isn’t configured use setspn to register.
setspn -A http/webapp.domain.local computername
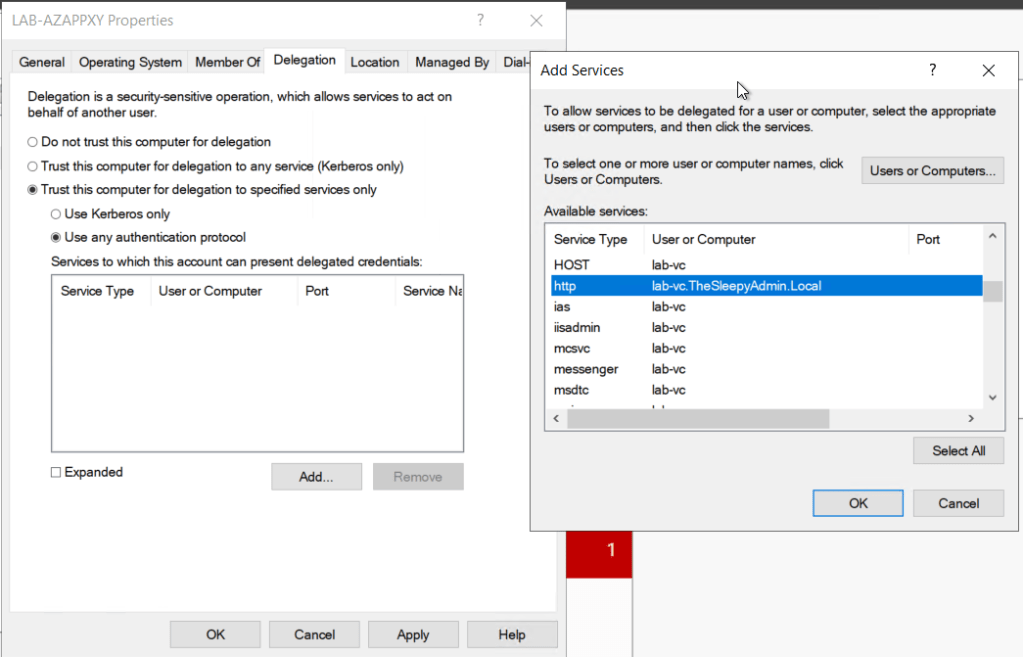
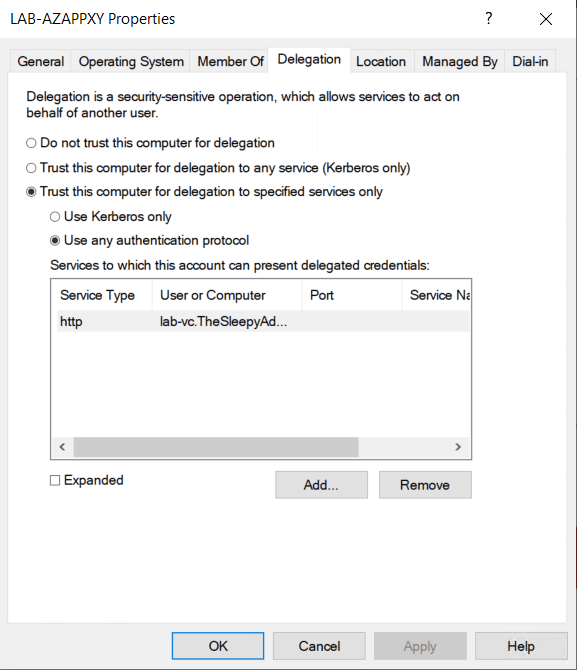
The next step is to configure the delegation on the Azure application proxy connector server.
Go to the server object in AD, open the properties and go to delegation.
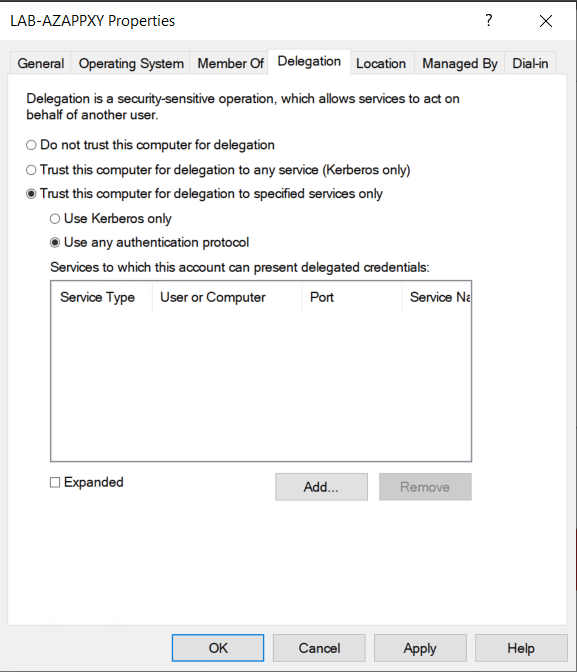
Click add and select the computer or user account that has the SPN that will be used and select the service.
The last step that I had to do was add the server to Windows Authorization Access Group so that the connector could have read access to TokenGroupsGlobalAndUniversal users attribute in AD.
When I didn’t have the server in this group I was getting SPN issues.

Next we need to configure SSO in Azure Enterprise app. Logon to Azure
Azure Active Directory > Enterprise applications > App
Select Single sign-on and Windows Integrated Authentication
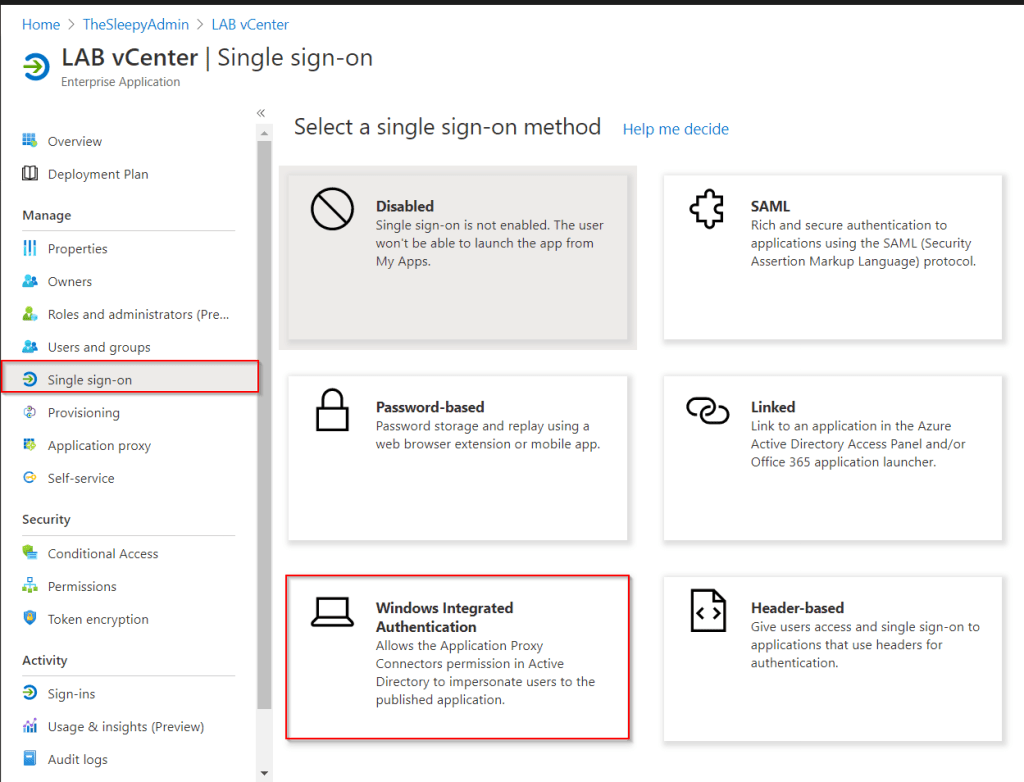
Put in the internal SPN that was configured earlier and set the delegated login, Our app uses samaccount name so I used On-premises SAM account name.

Once the above is completed close all open session to Office 365 / Azure AD and re-signed in to the external URL for the application proxy and the application should now signed in using SSO without have put in credentials a second time.
Thank you for this great procedure ! very helpful
LikeLike