On the last post we setup Azure Application Proxy to allow internal application’s to be made available externally using AAD integration.
To add additional security to the setup we can enable MFA for the group or users that will be allowed access.
To enable MFA we need to create a conditional access policy and enable on the application proxy.
First step Login to Azure
Go to Azure Active Directory (AAD)
Go to Enterprise applications

Select the Application proxy that will require MFA to be enabled
Once in the Application proxy go to Conditional Access and select New policy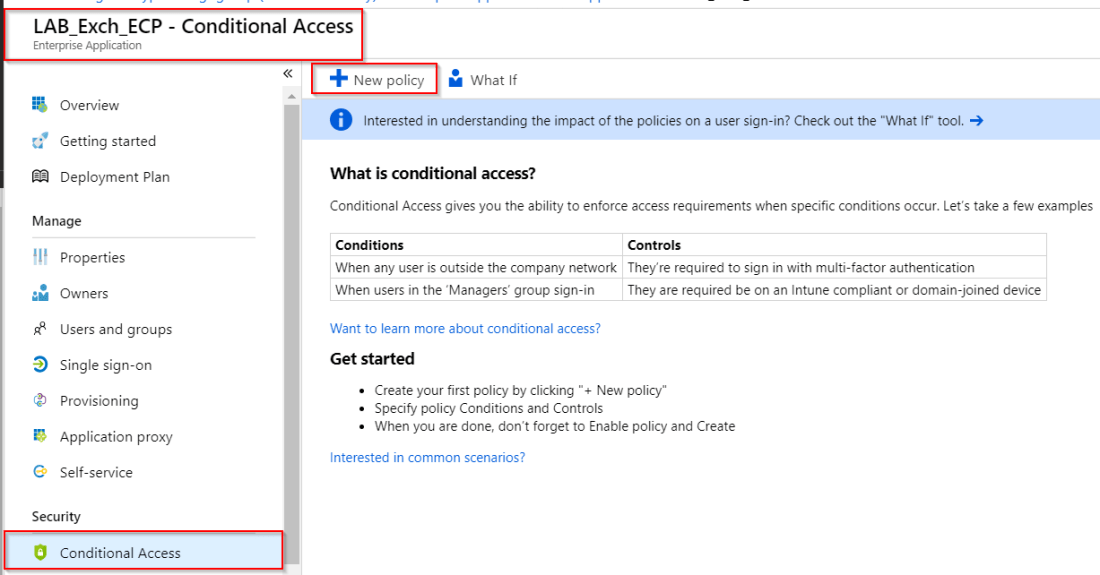
Give the policy a meaningful name as it will appear in the overall Conditional Access policy’s aswell as on the Application. This will make it easier to manage if there are multiple policy’s.
Then select Users and groups and select the required users or group
Next select the cloud apps that will require MFA in this case it is the Exchange ECP application that was configured previously
We will not setup conditions but if this is required it can be set to only allow access from certain devices types, location & sign-in risk level.
Next go to Access controls and then Grant tab. Select Grant access, tick Require multi-factor authentication and Requires one of the selected controls 
Last step is to Enable the policy

Click create at the bottom of the policy
The policy should now show and have tick under Enabled 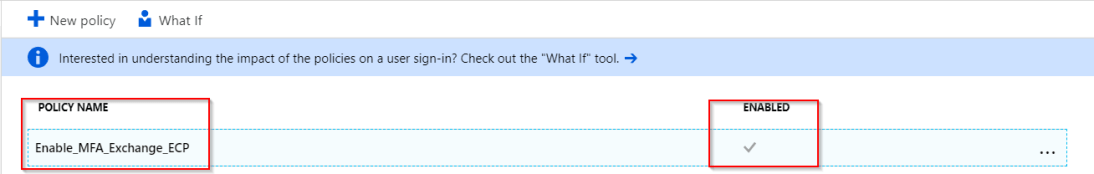
Now when we try to access the ECP Application proxy URL,
we should be prompted for MFA 
and asked to register and verify a device to be use for MFA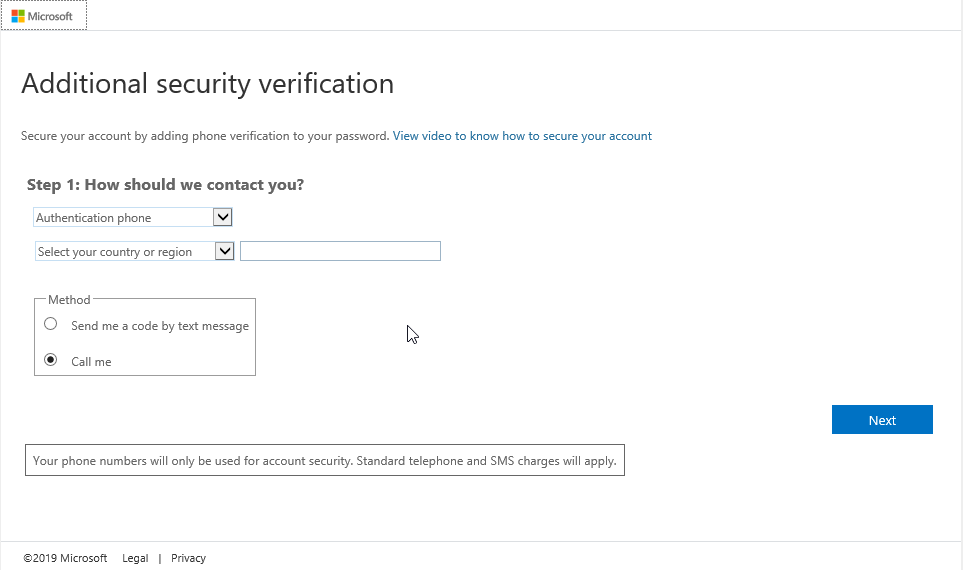
It is a good idea to enable MFA for application as it gives an additional layer of security.